CyberSPbSUT 2022 is a cybersecurity contest held as part of the federal project Information Security of the national program Digital Economy. This year, more than 130 students from 26 universities in St. Petersburg, Arkhangelsk, Petrozavodsk, Kaliningrad, and Syktyvkar came together for the contest’s qualifying round, which took place at the university’s Support Center of the National Cyber Testing Ground.
During this round, student teams of up to five members had to remotely monitor and record all cyber attacks performed by intruders. As a result, 47 students from 10 universities of St. Petersburg, Arkhangelsk, Petrozavodsk, and Kaliningrad advanced to the next round where they were offered to solve a similar task. Yet this time, the intruder managed to hack the infrastructure of a fictional company and encrypted their portal and server. The teams had five hours to investigate an ongoing attack by restoring the sequence of events and decrypting the data.
To solve the case, the participants turned to MaxPatrol SIEM – a software that collects Windows and Linux system logs and event reports produced by Suricata, an intrusion detection and prevention software. With its help, they found out that the hacker first scanned Windows ports and then tried to log into an administrator account via Remote Desktop Protocol (RDP). Once they got through, the attacker copied a section of the RAM associated with the lsass.exe process to access user data. By doing so, they got full domain admin privileges and were able to encrypt the file server and enterprise portal. Their next step was to hack passwords that the user “root” used on the portal and encrypt the platform, as well. While monitoring the intruder, the contestants had to thoroughly describe the attack process in their report so that the university’s lecturers and the testing ground staff could compare the results using scoring tools.

The ITMO))) team captain Georgy Gennadiev at the CyberSPbSUT 2022 awards ceremony. Credit: sut.ru
As a result, Test Team Please Ignore from the Northern (Arctic) Federal University, who earned 52 points, came third; Null_none from SPbSUT took the second place with 79 points, and ITMO))) brilliantly solved the task in three hours and scored 96 out of 100, thus winning the gold at CyberSPbSUT 2022. The winning team includes students from ITMO’s Faculty of Secure Information Technologies. The winners are Georgy Gennadiev, Egor Pereverzev, Nikita Chelnokov, and Artur Serdyuk, fourth-year Bachelor’s students, as well as Timur Abdullin, a first-year Master’s student. All are regular participants of specialized contests. In particular, they participate in the Capture the Flag (CTF) competition, the main task of which is to protect a server from attacks and capture the server of the opponent. Georgy Gennadiev and Nikita Chelnokov are also members of the FaKappa team.
“All of us either were or still are pen testers, that is, specialists who test apps and infrastructures by breaking into them and thus expose their vulnerabilities and offer ways to fix them. We all knew each other before the competition. However, we’ve never been on one team. I believe we won because we work well together and understand each other perfectly,” says Georgy Gennadiev, the team captain.
As noted by Georgy, CyberSPbSUT 2022 was not like any other contests, say, the First Intercollegiate Cybersecurity Wargames. This year, the contest’s tasks were more complex and participants could communicate with each other only verbally.
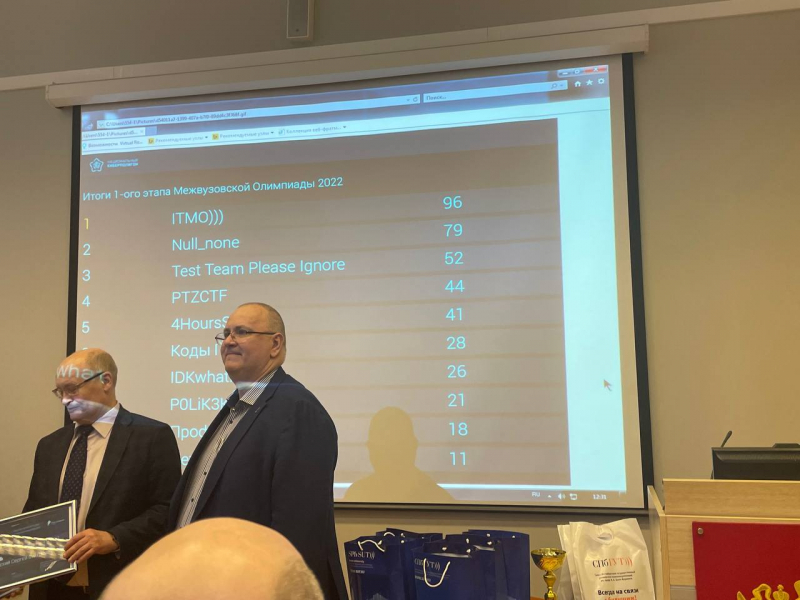
The CyberSPbSUT 2022 results table. Photo courtesy of Georgy Gennadiev
“We struggled most with decrypting Windows as for some reason our Suricata network analyzer would not show us HTTP requests and we had to find our way around to get an encryption key for the operating system. Finally, we realized where we could find it – system logs. What’s more, I’m on the FaKappa team. Some of my teammates are from ITMO but there are also those who study at St. Petersburg State University and SPbSUT. So, it was even harder for me knowing that I was competing against my teammate who was there representing their university,” notes Georgy Gennadiev.
The winners of the contest received certificates and special prizes from SPbSUT and the National Cyber Testing Ground, not to mention an opportunity to compete with the best teams from the Central, Volga, Siberian, and Far Eastern Federal Districts.
“Not only did the contest become our ticket to OpenBonch 2022 but it also gave us a chance to expand our expertise. Getting a practical insight into security strategies was a nice change of pace for us since we mainly deal with cyber attacks and only knew how such strategies work in theory,” shares Georgy Gennadiev.





